Past few weekend, some of the most popular websites were detected to be operating a script that lets the sites to mine users extra CPU power for the cryptocurrency, as denoted out by users on Twitter. The distressed websites incorporated was showtimeanytime.com, but it has been removed following reports from Gizmodo and other web portals. The crypto mining .js file is called CoinHive, and according to the site, it was made as an option to banner ads as a different way for website owners to get throughout disturbing ad-blockers. Some ad-blockers have now added coin-hive.com on the record of the banned.
What is CoinHive / a Website crypto miner?
The script mines the cryptocurrency known as Monero. Monero is an anonymous version of Bitcoin because the user can purchase it offline with cash. Thirty percent of the profits would go to coin-hive.com, while the websites using the service, like The Pirate Bay and Showtime keep the rest.
How does it work?
CoinHive works as a JavaScript miner for the Monero blockchain. You embed the miner (the .js file) into your website, and your users run the miner directly in their browser. That determines you are forcing users to “solve” a Captcha and when they click the “Verify Me” option, the CoinHive JavaScript API uses the user’s CPU power for a brief moment. Coin-hive.com also has a short link URL API available, which works similarly. Visitors mine XMR for you in correspondence for enjoying an advertising-free activity on your website. In other words, website owners can decide to reward users with the in-game coin or any other consideration of their choice. Here are some of the possible remunerations users might enjoy:
- Better video streaming speeds
- The ability to download a particular file, or unlock access to a specific folder
- Allow users to enjoy ad-free surfing
- Credit in-game currency or objects to the user in exchange for their CPU power
It is packaged into a JavaScript API. You can view the system in action at the developer’s community website here: coin-hive.com
Good and Bad Aspects of using stealth techniques of bitcoin mining on a website:
CoinHive seems to have lighted it’s life reasonably innocently. As a tool, it could be used by website owners to produce additional income rather than utilizing ad banners. It is primarily, a Java library that can be added to the website which will use a portion of the visitors CPU to mine Monero when visited by a visitor. Once the user is no longer on the site, CoinHive will stop mining using their CPU. The Pirate Bay began pursuing CoinHive rather than having ad pennants on their torrent website. Users were informed of the trial and its entanglements but were soon dropped by The Pirate Bay due to negative feedbacks.
Despite the negative feedbacks encountered by the Pirate Bay, the developers of CoinHive produced an innovative piece of code which is genuinely progressive thinking. Grievously, such speculation has already been abused by cybercriminals. It is the different chapter in the rise in reputation in what is termed by researchers as “crypto-jacking”. Authors of Safebrowsers began abuse of CoinHive. Users, over 140,000 of them, who uses Safebrowsers, a chrome extension, noticed that upon opening their browser with the tool installed and their CPU mode was driven within the roof. It unmistakably noted by user’s when they saw a high performance in drop on their devices. It resulted in accusations being made and further research be conducted by third parties. Upon a principal evaluation, it could be easily comprehended that the developer had added the CoinHive JS library.
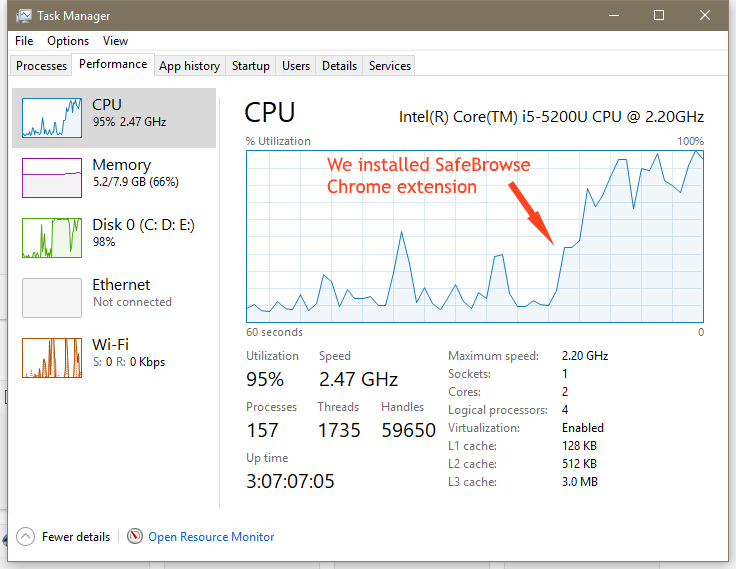
Another example of abuse can be found in some PC resources skyjacked for mining. According to research done by reporters at Bleeping Computer, once they began examining the extension it was quite quickly noticed that that the commandeered resources amounted to a large percentage of the overall performance. After opening the extension, they discovered that the Task Manager froze. Once the Task Manager began to operate, it reported that the tool was using a massive 60% of the CPU resources available.
How to find out a website is using CoinHive or any other Stealth Crypto Miners?
Check your CPU usage. Open the “resource monitor” on your computer to monitor if CPU usage is high. On a Mac, that’s “Activity Monitor,” and on Windows, it is the “Task Manager.” Ad-blockers can also help:
Your machine can be commandeered for mining by viewing a distinct website or having an infected notification displayed in it, as researchers at protection software vendor ESET have mentioned. If that is the case, once you close the tab, the mining will stop. For more peace of mind, you can block Javascript from running on a site known to be infected by directly using the default privacy and content controls in your browser. Another option is to disable from adblocker. Using Chrome as an instance, you would go to your extensions tab > find AdBlock and click: Options > customize > prevent an ad by its URL > in the text field that appears, input:
https://coin-hive.com/lib/coinhive.min.js
That’s all there is to it. Adblocker will protect your CPU from any websites running the CoinHive JavaScript file, and thus mining.
CoinHive made it easier for both blocking it and avoid blocking by releasing their JavaScript library on GitHub. Just including a couple of lines of code will originate the mining process and in same way, few easy steps will help users to block mining on their computer. There could be other websites doing the same. If you see the increase in your CPU activity as a user, you can block it by following the steps mentioned above. And as a web designer, you can add it to your websites. Here is the GitHub page of CoinHive cryptocurrency miner:
https://github.com/cazala/coin-hive.
If you want to learn more about CoinHive, Crypto Miners in general or require help setting it up on your own website, just toss me a message.
